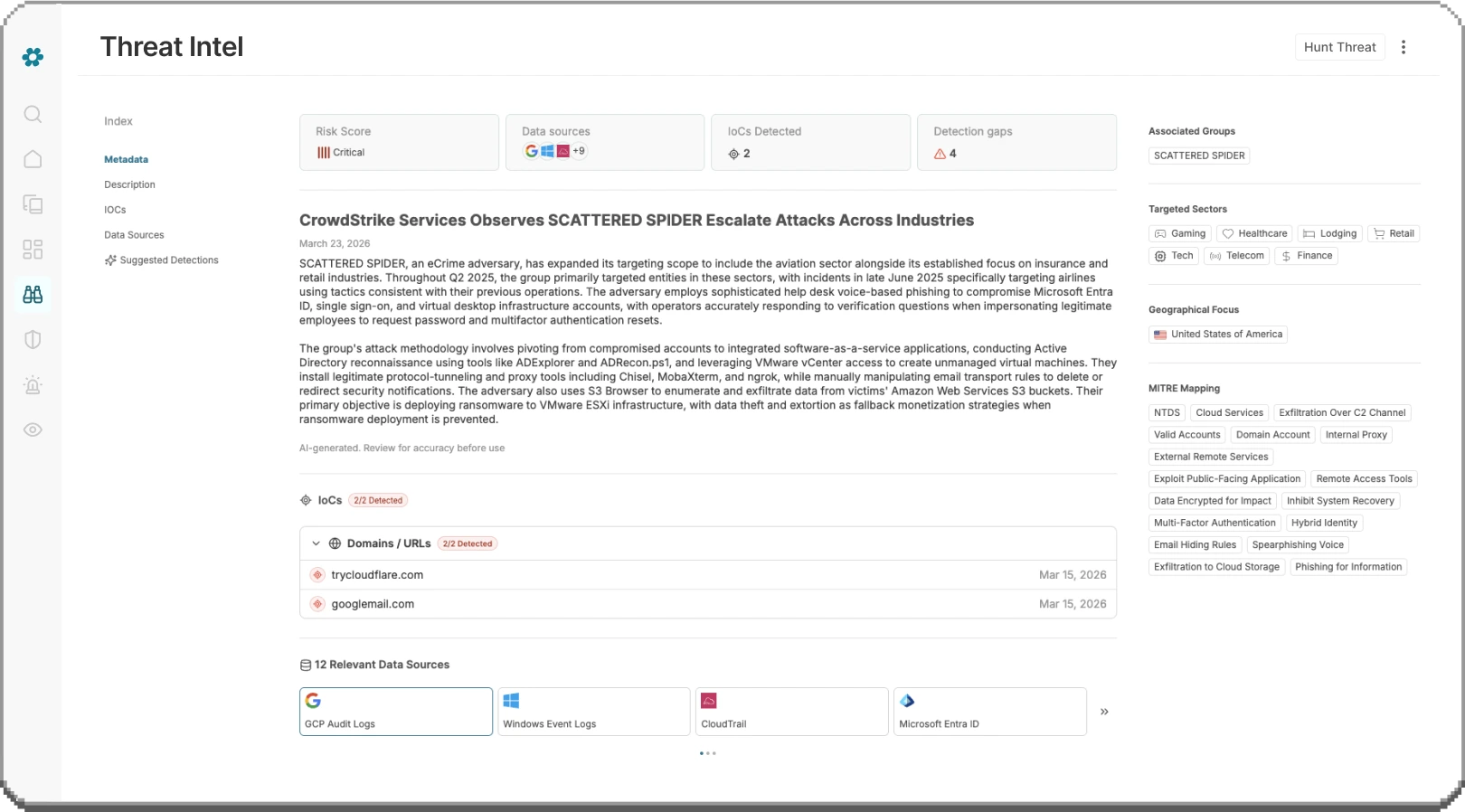
The Operating System for Agentic SecOps
AI is only as powerful as the visibility you give it. Vega's Security Analytics Mesh delivers complete visibility, enabling you (and our agents) to detect, investigate and triage across every data source - no ingestion, no migration, no gaps.

Your SOC runs on compromises you never planned for.

This is your SOC on the other side.
MttD & MttR goals achieved.

Your analysts hunt for threats, not data.
No more logging into four consoles to answer one question. No more missed alerts because they fell through a coverage gap. Your teams (and AI) have full visibility and context for every task.

Your detections adapt with your environment.
Unified Detection Engineering against every data source with continuous assessment and optimization of detection coverage, precision and relevance
Your SIEM bill stops growing.
Unlock the path to cost reduction by gradually adopting low-cost object storage alongside or instead of the more expensive, more complex alternatives - without the security trade-offs.
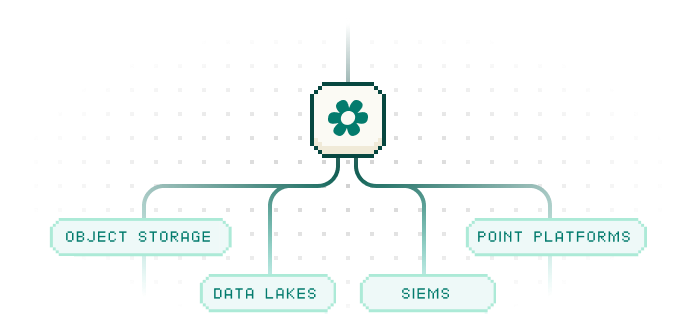
Unlock your telemetry. Decouple Analytics from Storage.
Unleash the SOC.
Legacy platforms demand ingestion of everything into their cloud. Vega frees you. Store it wherever makes sense for you.
Think of it as the Operating system your SOC runs on: it finally enables the security outcomes you want without the logistical nightmare you don't. Vega works with your architecture, your cloud, your needs.

Three layers. One continuous security operations loop.
Never static.
Vega’s Security Analytics Mesh is a federated analytics layer that connects to your data wherever it lives, without moving anything. Vega runs queries and detections across data in place, normalizing automatically to immediately return results. Finally, full coverage.
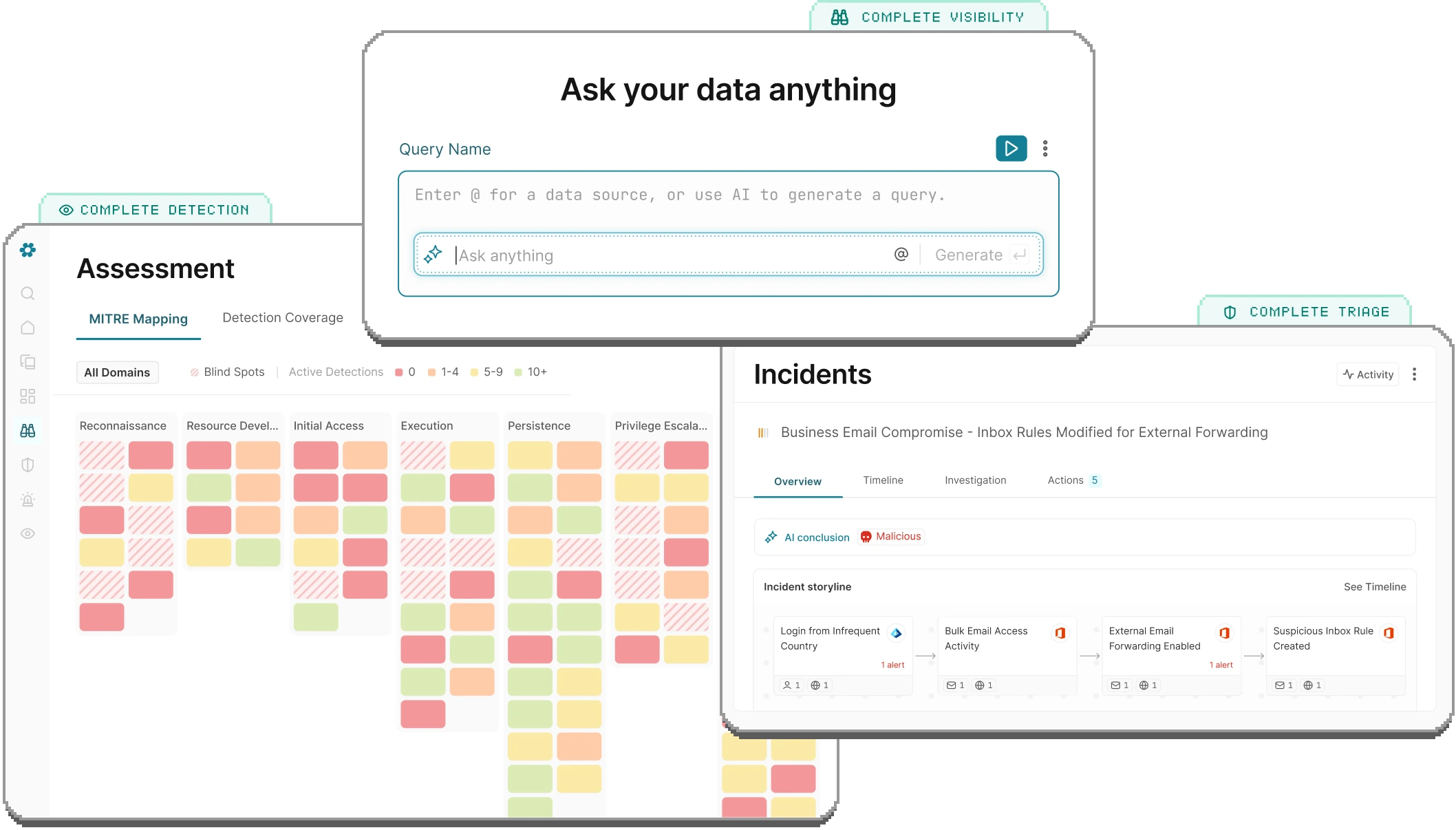
Complete Visibility
AI-native security analytics across all of your data (SIEMs, cloud logs, data lakes and even object storage) without moving any of it. No gaps. No blind spots. No compromises.
Complete Detection
Unified AI-powered threat detection that runs across data sources simultaneously, with continuous assessment of detection coverage, accuracy, and relevance. Detection that scales with you.
Complete Triage
Automate investigation, correlation, and enrichment with AI triage that can see raw logs and give you the full picture. Improve analyst efficiency and reduce Mean-Time-To-Respond with insights that continuously improve your detections.






























We wouldn't believe it either.
See for yourself how Vega makes your detection and analytics goals a reality, without modifying a thing in your existing stack.